Table of Contents
TogglecPanel is not just a web interface. It is a privileged orchestration layer with root-level control over web services, mail servers, DNS, databases, SSL provisioning, and account isolation. Because of that position in the hosting stack, licensing integrity is not merely a billing detail — it is a security and operational control.

This article provides a technical, operational, legal, and business-level analysis of what actually happens when cracked or fraudulent cPanel licenses are used.
1) What a cPanel License Actually Is
A legitimate cPanel license is:
- A legally binding software agreement (EULA)
- A server-identified license tied to IP or authentication
- Continuously validated through official verification mechanisms
- Required for updates, patches, and support access
When a license validates successfully, the system:
- Receives security updates
- Receives feature updates
- Maintains compatibility with operating system upgrades
- Retains access to vendor support
If license validation fails, update channels and official support are disrupted.
2) How Cracked Licenses Typically Work (Technical Overview)
Cracked licensing setups commonly rely on one or more of the following:
- Modified binaries that bypass license checks
- Firewall rules blocking outbound validation endpoints
- Hosts file manipulation redirecting license servers
- Injected scripts that spoof validation responses
These modifications operate at root level. That means the trust boundary of the entire system is altered.
Even if the system appears stable, the control panel is no longer running in a vendor-verified state.
3) Technical Security Risks
A) Tampered Software Integrity
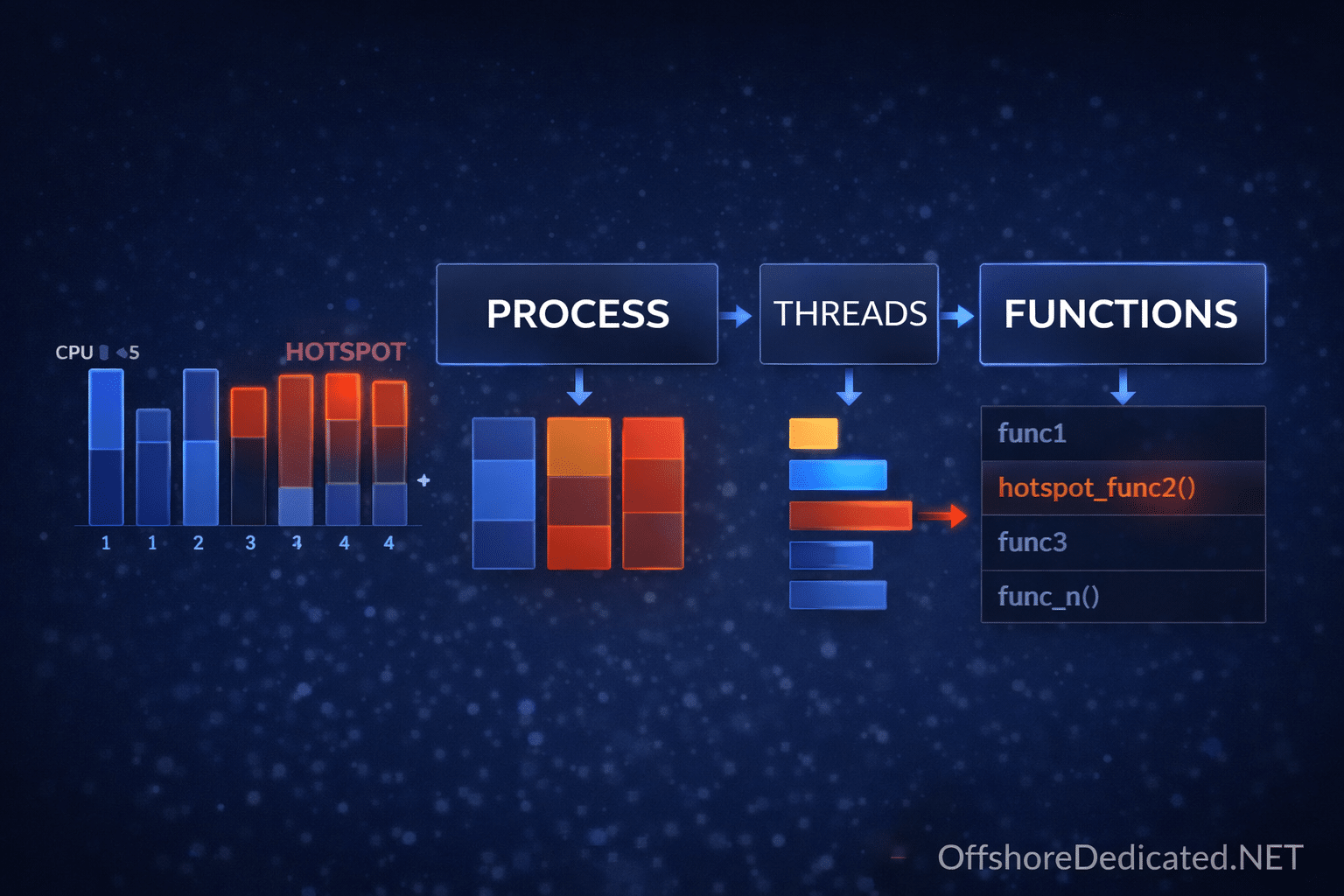
Any binary modification introduces unknown code paths. In hosting environments, this risk is amplified because cPanel manages:
- Apache/Nginx configuration
- Mail services
- DNS zones
- Database credentials
- User account isolation
A compromised control panel can expose all hosted accounts simultaneously.
B) Patch Denial and Vulnerability Exposure
Security patches are delivered through official update channels. If validation is bypassed:
- Critical CVE patches may not apply
- Update systems may silently fail
- Version compatibility breaks over time
Outdated control panels become predictable targets.
C) Supply Chain Trust Failure
Running altered software removes vendor signature trust. You cannot verify:
- Code authenticity
- Update integrity
- Security response timelines
In professional infrastructure, supply-chain integrity is foundational.
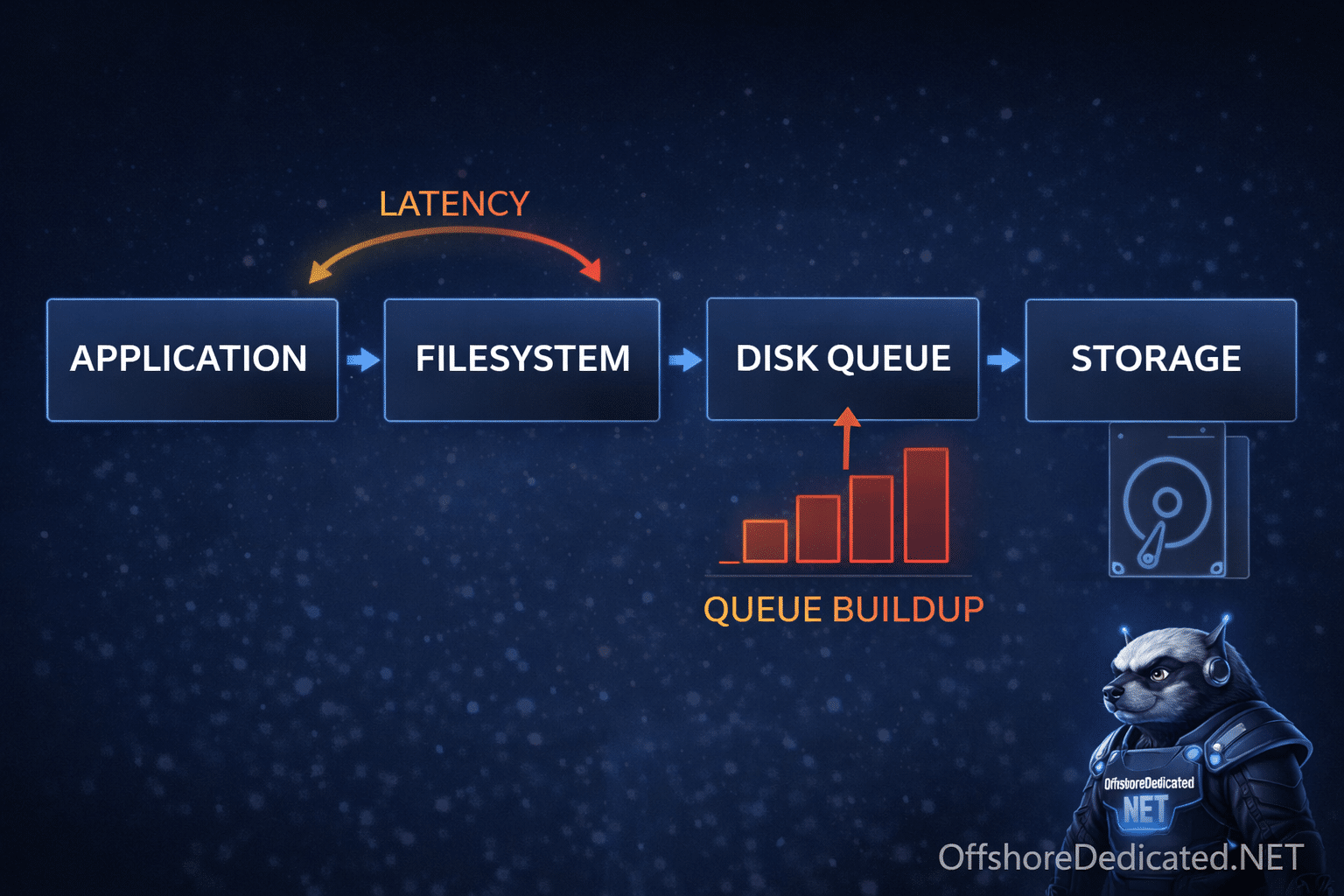
4) Operational Instability Risks
cPanel tightly integrates with the operating system. When licensing is tampered with, the following issues commonly emerge over time:
- EasyApache build failures
- Service restart loops
- Mail delivery instability
- SSL automation failures
- Incompatibility with AlmaLinux / CloudLinux updates
Because the control panel orchestrates services, failures cascade across the stack. Our analysis of control panel architecture and resource overhead explains how orchestration layers influence server behavior.
For a deeper understanding of how control panels influence system behavior, review our analysis of control panel architecture and resource overhead.
5) Legal & Contractual Exposure
Using cracked licensing violates:
- The software license agreement (EULA)
- Copyright protections
- Potentially data center acceptable-use policies
Consequences may include:
- License termination
- Service suspension
- Refusal of vendor support
- Legal claims depending on jurisdiction
Even if enforcement is rare, the exposure exists contractually.
6) Business & Reputation Impact
The cost of a compromised control panel exceeds the cost of legitimate licensing.
Risks include:
- Client data exposure
- Blacklisted IP addresses due to mail abuse
- SEO penalties after malware injection
- Forced emergency migrations
- Loss of customer trust
Hosting businesses depend on perceived reliability. Whether deployed on isolated dedicated hardware or virtualized Cloud infrastructure, licensing integrity directly affects service stability.
Running altered core infrastructure undermines that perception.
7) Real-World Scenario (Anonymized Example)
A small hosting provider purchased a “lifetime discounted” cPanel license from an unofficial source.
The implementation included:
- A firewall rule blocking outbound license verification
- A modified binary to prevent validation failure
Initially, the server functioned normally.
Over time:
- Automatic updates stopped applying security patches
- A known mail-related vulnerability remained unpatched
- Attackers exploited the outdated component
- The server began sending spam
- The IP range was blacklisted
- All hosted accounts required password resets
- Emergency migration to a clean server was required
The direct costs included:
- Client churn
- Reputation damage
- Recovery labor
- Downtime losses
The total operational impact significantly exceeded the cost of legitimate licensing.
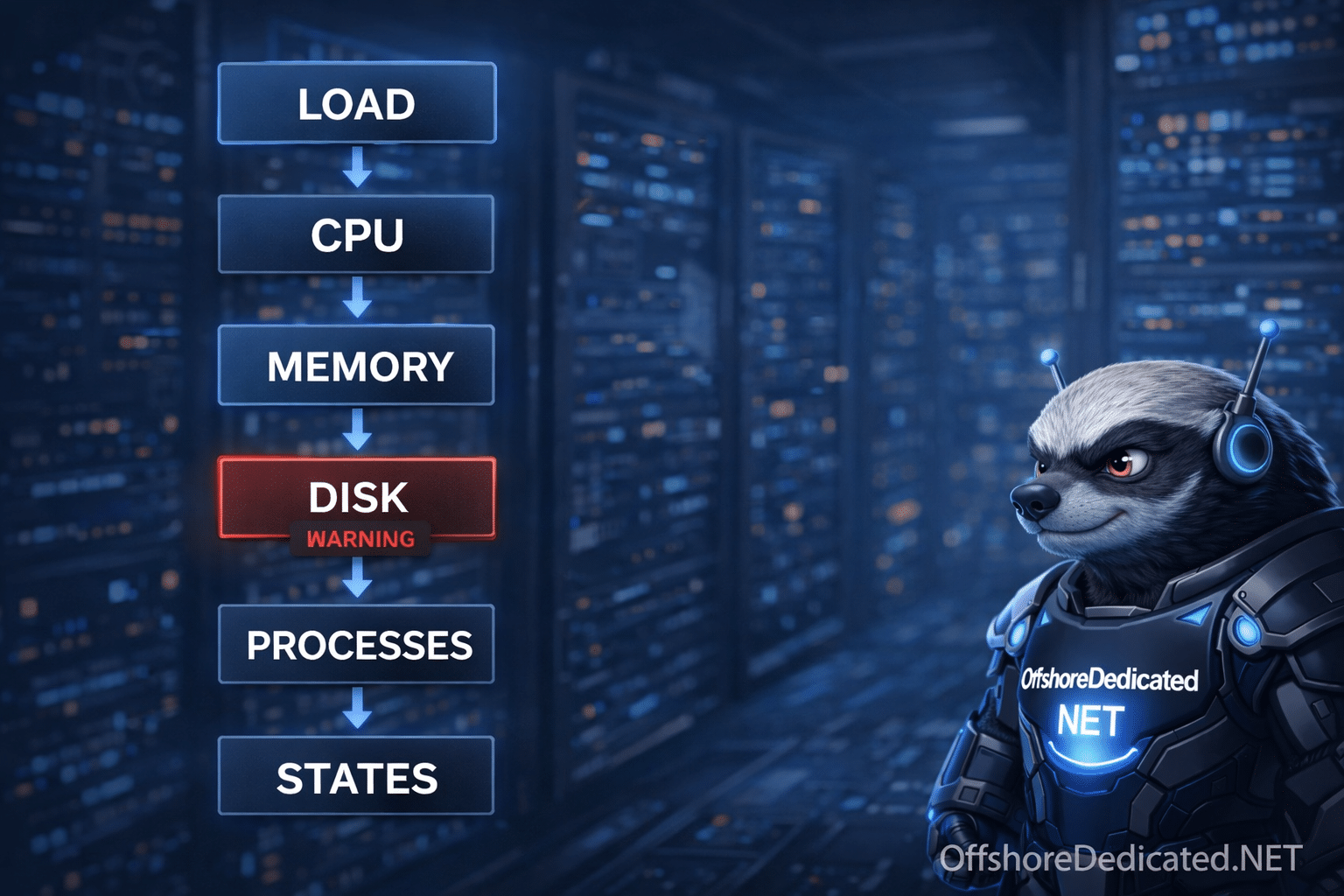
8) Detection & Recovery If You Discover a Cracked License
If you suspect licensing irregularities:
- Verify license status through official channels
- Remove firewall rules blocking validation endpoints
- Backup all accounts immediately
- Reinstall the operating system from trusted media
- Install cPanel using official repositories
- Restore accounts from clean backups
In high-risk cases, assume root-level compromise and rebuild from scratch. For system-level verification and service inspection during rebuild, review our guide on Linux command diagnostics in hosting environments.
For OS-level verification steps during rebuild, review Linux command diagnostics in hosting environments.
9) Ethical Infrastructure Positioning
Professional hosting infrastructure relies on:
- Verified software supply chains
- Supported update channels
- Transparent licensing compliance
- Predictable security response
Legitimate licensing is not just legal compliance — it is infrastructure hygiene.
Final Assessment
Cracked cPanel licenses introduce three categories of risk:
- Technical security exposure
- Operational instability
- Legal and business liability
Because cPanel operates at the control layer of the hosting stack, any compromise at that level affects every hosted account.
In infrastructure management, integrity at the control layer is non-negotiable.